SonicWall network security solutions provide unified protection for SMBs and branches via high-performance Next Generation Firewalls. The range spans from TZ Series tabletop units to NSa rackmount appliances and Virtual Firewalls for cloud environments. Centralised management ensures seamless control over SonicWall Switches and Wireless Security via WiFi 6 Access Points, creating a fully integrated branch ecosystem.
The Advanced Protection Suite features the Capture Security Appliance (CSa) for on-premises threat analysis and RTDMI technology to block zero-day malware. Secure Remote Access is facilitated through high-speed VPNs, while dedicated Licenses and Support ensure continuous firmware updates and 24/7 technical assistance. Comprehensive Accessories, including SFP modules and mounting kits, allow for flexible multi-gigabit hardware deployment. These multi-layered defences safeguard infrastructure against ransomware while optimising traffic through integrated SD-WAN.

|
The latest SonicWall TZ series, are the first desktop form factor next-generation firewalls (NGFW) with 10 or 5 Gigabit Ethernet interfaces. The series consist of a wide range of products to suit a variety of use cases. Designed for small, mid-sized organizations and distributed enterprise with SD-Branch locations, the 7th generation (Gen 7) TZ series delivers industry-validated security effectiveness with best-in-class priceperformance. These NGFWs address the growing trends in web encryption, connected devices and high-speed mobility by delivering a solution that meets the need for automated, real-time breach detection and prevention. |
|
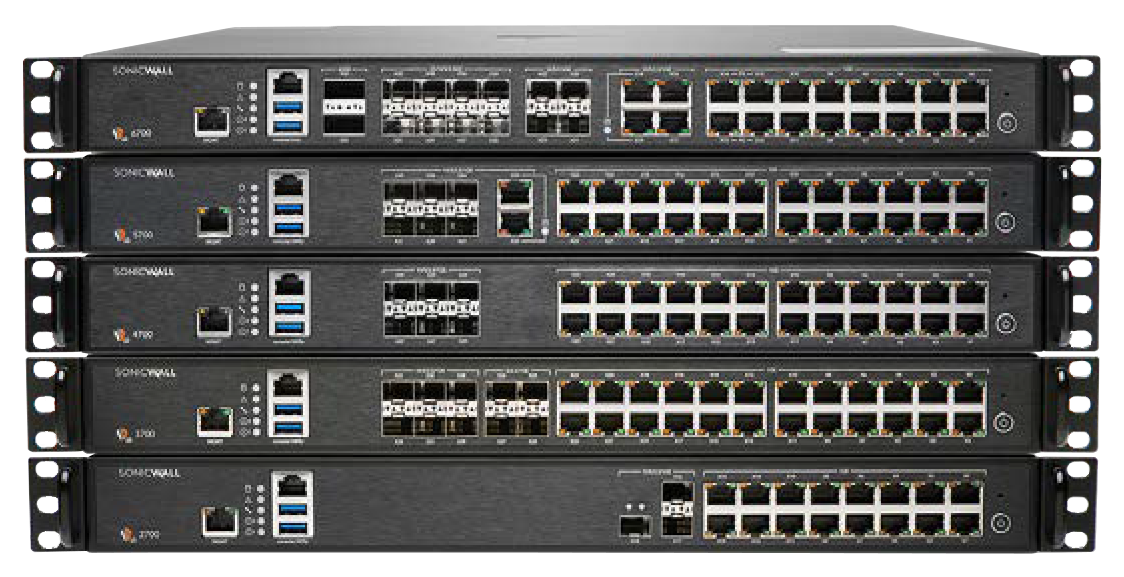
SonicWall Next-Generation Firewalls (NGFW) deliver enterprise-grade protection for small, mid-sized, and distributed organisations. Featuring real-time threat prevention, SD-WAN, Zero-Touch Deployment, and seamless cloud management, these firewalls safeguard networks against advanced cyber threats while optimising performance. Ideal for businesses seeking cost-effective, scalable security solutions. |

|
The SonicWall® Network Security Virtual Series (SonicWall® NSv Series) is SonicWall’s virtualized next-generation firewall appliance that provides Deep Packet Inspection (DPI) security and segmentation in virtual environments. |

|
SonicWall’s 600 series access points (APs) use 802.11ax - the most advanced technology available - for superior performance in high-density, multi-device environments. In addition to performance, these APs offer a number of additional features that provide an enhanced experience, as well as deliver best-in-class security that you expect from SonicWall. |

|
The SonicWall secure switch solution delivers unparalleled performance, security, manageability and performance in an enterprise-grade, sleek form factor. This enables businesses – big or small, to undergo digital transformation and keep pace with the changing network and security landscape. |

|
SonicWall Secure Mobile Access (SMA) is a unified secure access gateway that enables organisations to provide anytime, anywhere and any device access to corporate resources. |

|
SonicWall SonicWave series wireless access points (APs) combine high-performance IEEE 802.11ac Wave 2 wireless technology with flexible deployment options. These APs can be managed via the cloud using SonicWall WiFi Cloud Manager (WCM) or through SonicWall’s industry-leading next-generation firewalls. The result is a solution that could be untethered from the firewall to provide a superior experience for WiFi users that’s as secure as any wired connection. |

|
The SonicWall Capture Security appliance™ (CSa) brings Capture Advanced Threat Protection™ (ATP) and sandboxing malware analysis to on-premises deployment scenario. |

|
Various SonicWall Support options include:
Licensing covers wireless access points across different levels of security and terms offering 1, 3 and 5 year options. |

|
Explore SonicWall's range of Accessories including; Power Supplies and fans, Modules, PoE Injectors , Accessories and Mounting Kits available at Comms Express |















