
Cybersecurity hinges on robust passwords. Breaches expose sensitive data, and cripple even secure systems. This guide explores password best practices to fortify your digital defenses.
Key Takeaways:
- Length matters: Aim for 12+ characters for enhanced security.
- Mix it up: Combine upper/lowercase letters, numbers, and symbols.
- Ditch the dictionary: Avoid personal details and common words.
- Uniqueness is key: Craft unique passwords for each account.
- Regularly refresh: Update passwords periodically to maintain protection.
Q: What are some essential tips for creating strong passwords?
A: The article recommends using a minimum of 12 characters, incorporating a mix of upper/lowercase letters, numbers, and symbols, avoiding personal information and common words, creating unique passwords for each account, and regularly updating them.
Remember, even the strongest password can be compromised if it’s leaked or phished. Be mindful of where you enter your password and practice good security hygiene!
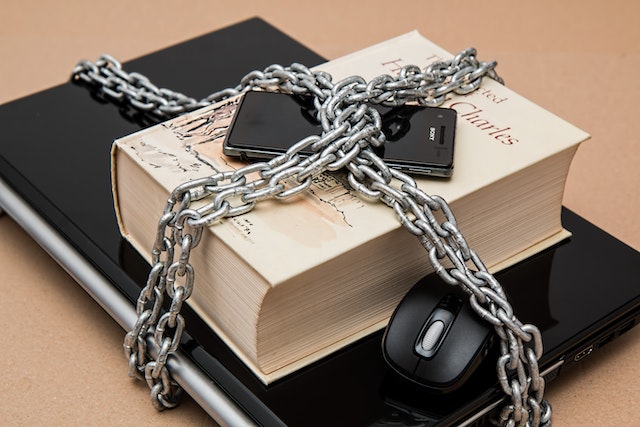
You could have the best security in the world protecting your network.
You could have all the latest software and the best firewalls.
But if your network passwords are weak, it can all come tumbling down.
Using strong passwords across all parts of the network is a vital step to keeping data secure. It’s a critical and simple step in Network Security best practices. While a strong password alone, won’t protect you, a weak password might bring down even the most sophisticated system.
Here at Comms Express, we know that it can be tricky to remember a plethora of passwords. So, we’ve created a guide to help you protect your computer network, and not be constantly locked out of your account.
Content
Why Do You Need A Strong Password
How Hackers Abuse Weak Passwords
11 Top Tips for Strong Password
Creating a Culture of Strong Passwords
Why Do You Need A Strong Password
In 2002, Gary McKinnon hacked into the United States military and NASA networks. The US government claims he deleted files, paralysed networks and caused $700,000 of damage.
He said he was looking for evidence of UFOs.
How?
In a 2006 BBC interview, McKinnon claimed he used a Perl script to find blank passwords. He implied that many computers on the network had default passwords.
So if weak passwords can bring down an expensive, high-security military network, imagine what it would do to businesses without sophisticated technology.
GDPR
If four letters could strike fear into business owners, it might be GDPR. Under European guidelines, all personal data needs to be kept secure. Breaches in security could mean your business is fined millions of pounds.
Keeping strong passwords is a key part of GDPR. This can help your company prevent breaches of security, which will stop people from accessing and downloading personal information.
How Criminals Abuse Weak Passwords
There are many ways that hackers will try to access your account. While there are some very sophisticated methods that high-end hackers may use, there are some widespread tactics that most hackers will use, and often find results due to poor password security.
Phishing
Some phishing attacks will happen when a person attempts to create an authentic-looking fake website, email or other media type to steal personal data. This could vary from an email asking for you to enter your details on a fake website, to a person calling up pretending to be your bank.
99.9% of the time, a company does not need your password to offer support. Their systems will have ways to be able to log in to your account from their end, or they will talk you through the issue over the phone.
Brute Force Attacks / Dictionary Hacking
These attacks are when hackers attempt to log into an account or network by using common passwords or words found in the dictionary. Attackers will start with passwords such as “Password” or “123456”. They will then move on to dictionary words like “love1”, “Dog123”, “welcome”. Dictionary attacks are probably the most common.
The attacker will flood the password box with these hacks to attempt to gain access, sometimes by logging thousands of attempts a minute.
Mass Theft
Once a hacker has one password, they will assign it to your email account. They will run a script which allows them to try the email and password combination across the most popular websites to find more sensitive information. So, that means you need to use different, strong passwords for every account.
10 Top Tips for Strong Passwords
1. Use a minimum of 12 characters
With strong passwords, longer is better. Many hackers will start with shorter passwords, as they are easier to hack. The longer your password, the less likely it will be for a brute-force hacker to get an exact match. It is also more difficult for people watching you to work out which buttons you are hitting.
2. Use Uppercase and Lowercase letters
Using upper and lower-case letters is a useful way to add a layer of strength to your password. Try to avoid using an upper case letter at the beginning, as this is a common trait of passwords. Scatter capitals and lowercase throughout your password.
3. Use Symbols and numbers
Symbols and Numbers add another layer to a strong password. Avoid using the symbols at the start and end of passwords, as this is a common trait in passwords.
Try to stick to common symbols, such as *, &, ! and %. Some website password fields struggle to pick up symbols like pipe keys (|).
4. Avoid words combinations directly from the dictionary
As we explored earlier, dictionary hackers will use a script which logs words from the dictionary into the password field. Therefore, avoiding words from the dictionary is advisable. Using fake words, names or real words but jumbled up is a much better way to create a strong password.
5. Avoid Obvious Substitutions
A common way to “strengthen” a password is to replace a letter with an obvious substitution, such as using an exclamation mark instead of “I” or “4” instead of “A”.
These simple substitutions will be checked by hackers as well so it may not be strengthening your password at all. Try to be more random with your letter substitutions if you go down that route.
6. Create Passwords Based On A Story
To help create memorable, strong passwords, you could use a story or song lyric to help you remember.
For example:
We always celebrate St Patrick’s Day in The Red Lion Pub on the 17 March!
This could become:
Wac$PDitRLon17m!
Or choose a string of random phrases to create a strong password. Such as:
SanchezCastleDonkeyBanshee
You can add some extra numbers and special characters to create a stronger password.
They are personal and easier to remember but are difficult for a hacker to guess.
7. Avoid Using Something That’s “No Big Secret”
Die-hard sports fan? Big fan of a particular band? Have a long-term partner?
If your social media profile picture is the logo of your favourite band, team or product, then avoid using those as passwords.
Hackers trying to get into a profile may seek to gather information such as birthdays, passions and family members to try to gain access to your profiles. To create a strong password, keep references obscure.
8. Use Random Characters
Another way to ensure unique passwords is to create passwords entirely randomly. There are strong password generators out there for generating passwords for you. Or you can just run your hand over the keyboard. You could always retroactively create a story around it, or use a password manager to store them.
9. Update your passwords regularly
Ensure that you update your passwords regularly. The recommended average is between 1-3 months. Make sure you aren’t just adding numbers on, you need to be changing them completely.
10. Never share your passwords with anyone…
Your passwords are your personal protectors. You shouldn’t be giving access to anyone who doesn’t need access. Phishing scams may try to trick you into handing over your password, but as a rule of thumb, never hand over your passwords to anyone.
There may be some times when it’s unavoidable. In that case, change the password before you give it to them. For example, you may need a company to log in to an account. Change the password to refer to that company, so it’s obvious you changed it. Then, when they are done, return to a strong password.
Using Password Managers
The best and safest way to store passwords is in your brain. However, for those who have a vast amount of logins, or struggle to remember them, a password manager may be for you.
With a password manager, you only have to remember one master password, which needs to be the strongest password as you can make.
Many will have an internal random password generator to help you generate passwords for your account. You then log into the secure password manager on your PC or mobile and it will automatically populate the login fields for you.
Password managers such as LastPass and 1Password are great places to start with looking for a secure, strong password manager.
Creating a Culture of Strong Passwords
The hardest thing to do is to convince your staff to use strong passwords. Creating a business-wide culture of ensuring passwords are strong will be the key to securing your network.
If your company has an internal newsletter, you could place an article with facts and anecdotes about strong passwords. Make it fun and interesting. You will want people to take note.
You could also include strong password policies in the employee handbook if your company does training for recruits, ask them to put in some password training.
Roundup
So these are some of the best practices for creating strong passwords to protect your network. While a strong password is not the only way to protect your network, it certainly is one crucial step. Passwords are an important aspect of cybersecurity and are used to protect data and networks. It is important to use strong passwords that are difficult for others to guess or crack in order to prevent unauthorized access to your accounts and systems.
There are several ways to create strong passwords, including using a combination of letters, numbers, and symbols, avoiding using personal information such as your name or date of birth, and using different passwords for different accounts. It is also important to regularly update your passwords and not share them with others. By following these best practices, you can help protect your data and network from potential threats.
